In the world of government operations, information changes hands on a daily basis. Some of that information is public, readily available, and completely open. Other information is controlled in some fashion, from the largest “open secrets” that are easy to access, to more “top secret” information that is limited to a few thousand people across the country, to information available only to a Freedom of Information Act request, all the way to the information known only to the president and a few top aides.
Naturally, the higher the level of classification to the information, the harder it is to access and the stricter the controls over it. Truly secret information can be a very severe crime to share. On the other hand, some information is much more broadly available, as long as it’s handled in specific ways.
Perhaps the lowest level of classification that still requires any sort of specific handling is called CUI. What is CUI, though, and what are the regulations surrounding it? Let’s dig in.
 BLUF - Bottom Line Up Front
BLUF - Bottom Line Up Front
Controlled Unclassified Information (CUI) is information that is not classified but still requires specific handling under US government regulations. CUI comes in various categories, divided into Basic and Specified types. Standards like NIST 800-171 outline the minimum requirements for handling CUI. Service providers seeking to work with the government must familiarize themselves with these standards to ensure compliance and qualify for contracts, using tools and audits to maintain and prove adherence.
What is CUI?
CUI stands for Controlled Unclassified Information. It means that the information is not classified or secret, but it still falls under the governments jurisdiction and thus needs to be controlled in some fashion.
A good example comes from, of all things, a video game.
The video game War Thunder is a vehicular combat simulator. Players take control of a wide variety of war vehicles, from planes, UAVs, and helicopters to tanks, battleships, and more.
Critically, one area where War Thunder shines is an emphasis on realism, or at least a milsim level of “realism” that makes for a good video game. However, this has led to an interesting effect; people, often people in the military (and not just the US military), who have vehicles they work with, on, or around on a daily basis, and which they love deeply, want to see those vehicles represented accurately in the game.
To “help the developers” make “more accurate” versions of the vehicles – or to simply prove their case that a vehicle is over or under-powered – people have leaked CUI documents (and documents with stricter classifications) on the War Thunder public forums. This has happened several times; so often, in fact, that it’s almost become a joke.
Many of these documents are not classified, but are still controlled; they fall under the heading of CUI.
For the actual specific definition of CUI, you can read it from the mouth of the government itself:
“Information the Government creates or possesses, or that an entity creates or possesses for or on behalf of the Government, that a law, regulation, or Government-wide policy requires or permits an agency to handle using safeguarding or dissemination controls. However, CUI does not include classified information or information a non-executive branch entity possesses and maintains in its own systems that did not come from, or was not created or possessed by or for, an executive branch agency or an entity acting for an agency. Law, regulation, or Government-wide policy may require or permit safeguarding or dissemination controls in three ways: Requiring or permitting agencies to control or protect the information but providing no specific controls, which makes the information CUI Basic; requiring or permitting agencies to control or protect the information and providing specific controls for doing so, which makes the information CUI Specified; or requiring or permitting agencies to control the information and specifying only some of those controls, which makes the information CUI Specified, but with CUI Basic controls where the authority does not specify.” – National Institute of Standards and Technology, Information Technology Laboratory, Computer Security Resource Center Glossary
Quite a mouthful, right? Well, suffice it to say that it’s relatively simple and casts a wide shadow.
What Types of CUI Are There?
CUI actually falls into a bunch of different forms, of which there are two groups, 20 index groups, and 125 categories.
Let’s start from the bottom up. The 125 categories are things like “Water Assessments”, “Naval Nuclear Propulsion Information”, “Bank Secrecy”, “Whistleblower Identity”, and “National Park System Resources”. You can see the full list here.
As you can see, these have a very wide divergence in importance. Information about the national parks doesn’t feel like the same kind of information as information about nuclear propulsion, after all. We’ll get to that.
The 20 index groups are the headings for specific categories of information. So, for example, those five we picked above are:
- Water Assessments, part of Critical Infrastructure.
- Naval Nuclear Propulsion Information, part of Defense.
- Bank Secrecy, part of Financial.
- Whistleblower Identity, part of Law Enforcement.
- National Park System Resources, part of Natural and Cultural Resources.
Each of those broader index groups contains a variety of specific categories of information. Again, you can read it all on the linked page above.
Additionally, each specific category of information can be specified as either CUI Basic or CUI Specified. So, what are those?
CUI Basic
CUI Basic is basic controlled information. It’s information that is sensitive enough to warrant being controlled, but not so sensitive that it needs special protections above and beyond the baseline necessary for all CUI.
CUI Basic information is generally just labeled as CONTROLLED or CUI in the documents, but some kinds of information don’t have those labels easily available, so if you’re handling CUI, you’re expected to treat all relevant information with sensitivity.
All CUI Basic information needs to adhere to two interlinked documents. These are the FISMA (Federal Information Systems Modernization Act), specifically at the Moderate level, and the NIST standard SP 800-171. For the latter, see our recently-published guide for greater detail.
While those documents are nothing to scoff at, they’re, well, a high bar. It’s one set of information controls that you’ll need to meet and maintain.
CUI Specified
CUI Specified, on the other hand, is more complex.
This is for information that is controlled, but warrants tighter restrictions than basic CUI controls; however, it’s not so sensitive that it needs to be classified. It’s a sort of middle ground.
CUI Specified has an additional set of controls and protections on top of NIST 800-171. However, there’s a tricky detail here; each set of information falls under the banner of the agency that creates and controls the information. So for Naval Nuclear Propulsion Information, you’re looking at CUI information labeled SP-NNPI, controlled by the specific agency governing it (like the Department of Defense), and subject to additional controls.
The additional controls are created by a law or regulation and defined by the agency. So, different kinds of information, controlled by different agencies, will have different markings and different standards.
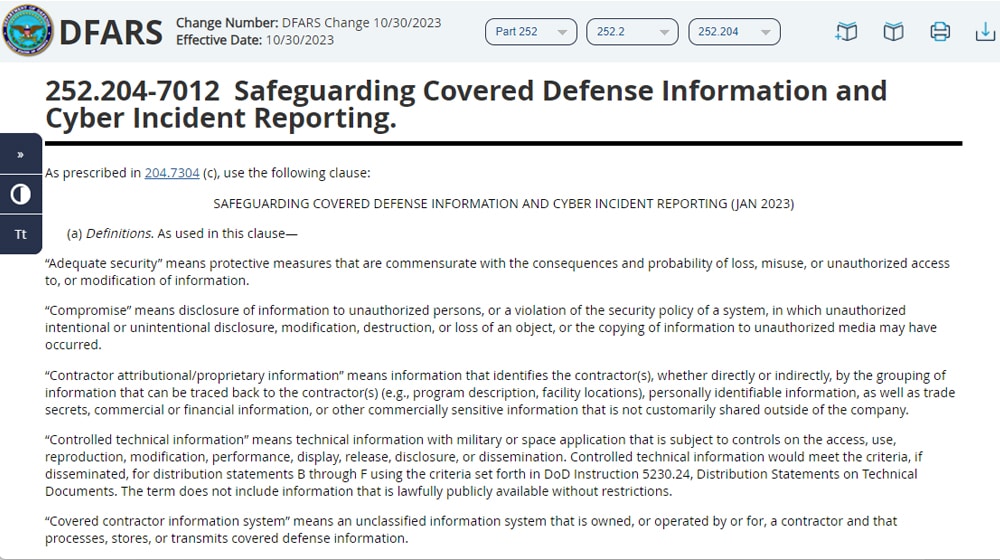
To use one example, the set of standards known as DFARS 7012 covers defense information. DFARS is the Defense Federal Acquisition Regulation Supplement, and it’s a huge set of additional guidelines, found here.
This is, as it says in the name, a supplement. You still need to comply with NIST 800-171 and other relevant standards, along with any specific additional standards necessary for the information you need to handle for your specific contract.
What Standards Must You Follow?
Identifying the set of standards you need to follow depends a lot on what you’re planning to do.
First of all, none of this matters unless you’re a current service provider to the US Government. Secondly, none of it matters unless you’re planning to work with the United States Government.
The Government employs a wide range of service providers, simply so they don’t have to reinvent the wheel and create their own clone services in-house; it’s a lot of additional time, expense, and effort they don’t need to save. The standards, like NIST 800-171, exist to give service providers a framework to follow to maintain a minimum level of security and confidentiality for government information.
So, if you’re a service provider and you have no plans to work with the government, you don’t need to care about specific standards like NIST 800-171.
Note: Even if you don’t plan to work with the government, it can be a good idea to at least familiarize yourself with what NIST 800-171 and other regulations entail. After all, good information security and good administrative practices are a boon to every customer, not just government contracts, and it’s just good practice, even if you don’t pursue CMMC certification.
Plus, by meeting and maintaining those standards, it’s easier to certify if you want to down the line to be able to qualify for lucrative government contracts.
If you plan to work with the government, your next step is to have some idea of what agencies you’re working with. You’ll very likely have to meet different standards depending on who you’re working with, be it the Department of Defense, the Department of Education, the State Department, or another agency.
From there, you can determine what kinds of information you’re likely to be handling, and what standards above and beyond the normal NIST 800-171 standards for Basic CUI you’ll need to implement.
You don’t have to do all of this alone, of course. The agency you’re looking to work with will be able to help, and there are a variety of tools available, including Google Workspace and our platform, Ignyte. With advanced tools by your side, you can help ensure compliance and maintain your status as certified to handle both kinds of CUI.
There are a lot of different potential subcategories and regulations surrounding specified CUI forms; you can read a full training document about those markings, how to read and interpret them, and how to apply them, here. Note that CUI can be applied to pretty much any kind of information; while you see it most often on standard documents, it can also be flagged on presentations, in emails, and more.
What Should You Do?
As a services provider that wants to engage with government contracts, the first thing you need to do is familiarize yourself with NIST 800-171. This is the bare minimum set of standards you’ll need to implement, the processes you’ll need to have in place, and the reactions you’ll need to have in the event of any sort of breach.
Once you’ve learned the guidelines and implemented them throughout your business, you can find a C3PAO (Certified Third Party Auditing Organization) like us to perform a comprehensive audit. Once you’ve had the audit performed, you’ll either pass or fail. If you fail, you need to readjust and reapply. Don’t worry; this happens a lot, and can be caused by anything from a typo in paperwork to a significant issue. There’s a reason the certification process often takes half a year or longer.
If you pass, then you’re able to apply for full certification. With that certification, you’ll be able to bid on contracts with the agency you selected for your certification. You can bid on contracts and be confident in your ability to maintain CUI security standards while working with the government.
You can also apply for further clearances to work with other agencies. Each agency has their own standards built up upon the foundation of NIST 800-171, including those CUI specified standards. However, that’s all additional steps you can take down the line. First thing’s first; you need to implement NIST 800-171.
Luckily, we can help. Our platform is a monitoring and auditing system that allows you to see at a glance how your company handles and maintains CUI standards, and if you have any shortcomings. If so, it helps give you the best route to fixing the issue, while maintaining compliance monitoring. We also help with other standards, including FEDRAMP certification, HIPAA information compliance, and much more.
If you’re interested in giving our platform a try, you have a few options.
- Reach out and contact us with any questions you may have. We can help you with anything from determining whether or not you even need certification, to how our platform can help.
- Click the button up top to request a demo of our platform today. You can see it in action and explore the information we can give you, so you can learn the ins and outs of the platform before you make a commitment.
- Click here to request a price sheet for your organization. Every CSP is different, and we aren’t a one-size-fits-all platform. We strive to provide the best service for you, so you can maintain the best security for the country.
Pick the option that best suits your needs; we’re standing by to help!
Max Aulakh is a distinguished Data Security and Compliance leader, recognized for implementing DoD-tested security strategies and compliance measures that protect mission-critical IT operations. His expertise was shaped in the United States Air Force, where he was responsible for the InfoSec and ComSec of network hardware, software, and IT infrastructure across global classified and unclassified networks. He also developed strategic relationships with military units in Turkey, Afghanistan, and Iraq. After his tenure with the USAF, Max played a pivotal role in driving Information Assurance (IA) programs for the U.S. Department of Defense (DoD). As a Senior Consultant for a leading defense contracting firm, he led a team that ensured data centers met Air Force Level Security audits for regulatory requirements like HIPAA, SOX, and FISMA. Currently, as the CEO of Ignyte Assurance Platform, he is at the forefront of cyber assurance and regulatory compliance innovation, catering to defense, healthcare, and manufacturing sectors. Max is also an esteemed speaker, having presented at several conferences on topics including cybersecurity GRC, medical device security, and cybersecurity perspectives in vendor management. You can follow him in LinkedIn here.


 BLUF - Bottom Line Up Front
BLUF - Bottom Line Up Front