Across the ecosystem of federal contractors, a majority of deployments tend to be relatively standard. 80% of them will be FedRAMP impact level Moderate, for example, and most will have a standard set of considerations and concerns, such that a lot of security controls can be automated.
It’s those outliers that make FedRAMP challenging. When a CSP has specific concerns that vary from the norm, they have to take extra care to ensure they’re doing everything right, and auditors will often give these areas extra scrutiny.
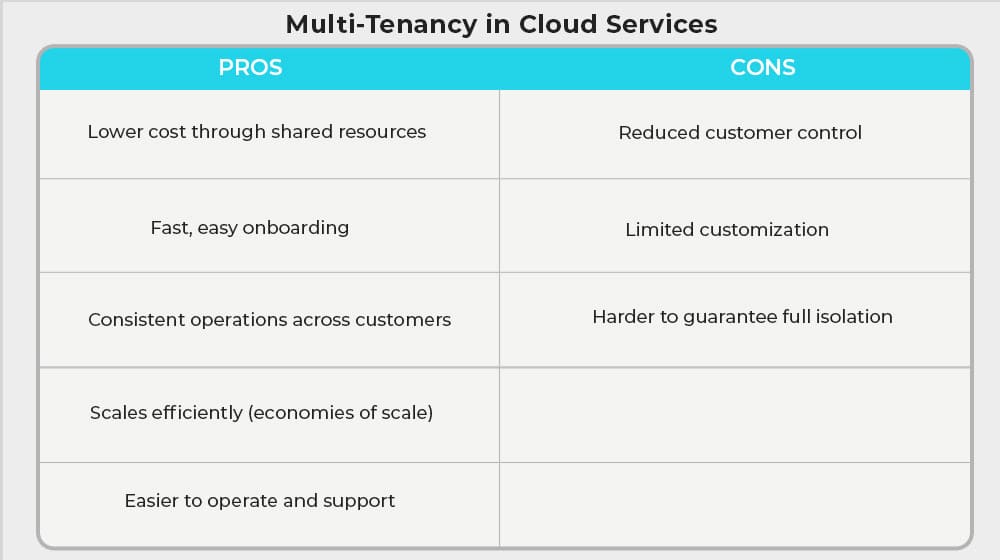
One of the more common sources of variance is tenancy. There are some specific concerns regarding whether you’re a single-tenant CSP or a multi-tenant CSP, and being prepared for those differences is critical. So, let’s talk about it!
 BLUF - Bottom Line Up Front
BLUF - Bottom Line Up Front
Most federal cloud deployments follow standard patterns; 80% meet FedRAMP Moderate. Outliers create extra auditor scrutiny. Tenancy; single versus multi; drives major differences. Multi-tenant offers lower cost, faster set up, and uniformity but gives customers less control and raises data isolation risk. FedRAMP permits multi-tenant at Moderate and High if controls ensure isolation and boundary protection. Key controls: strict access control, validated encryption, continuous oversight, rapid incident response, fast patch updates, and expert 3PAO support.
What is a Tenant in Cloud Services?
Understanding tenancy when it comes to FedRAMP first requires understanding tenancy in general.
Fortunately, the concept of tenancy is easy to understand, as it’s something nearly all of us have experienced at some point in our lives, even outside of the business and cloud spaces.
An easy metaphor for understanding tenancy is housing. Consider the differences between a stand-alone house you own and an apartment building. The house is a single-tenant building, where the apartment complex houses multiple tenants, each in their own distinct environments, but with some shared utilities and services (such as water, parking, and the like).
Note that despite the metaphor, this does not relate to multi-site certifications, which are focused on different physical locations for one business. Multi-tenancy refers to customer accounts on infrastructure, not business locations.
Tenancy in cloud services is much the same. A cloud-based business sets up its services to run on cloud infrastructure. If that infrastructure shares some resources with other businesses, they’re in a multi-tenancy situation. If the base infrastructure is solely for their use, they’re on a single-tenant structure.
When we talk about infrastructure in this case, it often means things like the base-level applications, the databases, and other near-metal elements of the infrastructure. It doesn’t necessarily mean the hardware itself, though it can.
This can apply from two perspectives for a CSP.
The first is from the CSP upwards, to the infrastructure they use. Many CSPs, for example, use services like Microsoft Azure or Amazon AWS. The choice of whether to invest in a single-tenant account or a multi-tenant account is one of the first the CSP will need to make. This is less relevant to FedRAMP for the CSP, however, since it would be the responsibility of the infrastructure provider to maintain their own version of FedRAMP security.
The second is from the CSP downwards, to their customers. The decision of how customers are managed, and whether those customers are able to buy into a single-tenant account, or if everyone is on a shared multi-tenant system, comes down to operational decisions. This is where all of the security controls and implementation relevant to the CSP’s FedRAMP deployment come into play.
If you’ve already guessed that a single-tenant setup is better for a CSP looking to achieve FedRAMP authorization, you will be unsurprised to learn you’re correct, so let’s talk about why.
The Pros and Cons of Multi-Tenancy in Cloud Services
If a CSP is looking to work with the government and achieve FedRAMP authority to operate, why would they still choose the multi-tenant route?
Multi-tenant services have a lot of advantages in a business and operational sense.
- They’re easy to onboard. Whether it’s setting up new customer accounts or just setting up their own account, it’s often as simple as a script or two being run and some configuration options being set, and it’s good to go.
- It’s cheaper. The biggest deciding factor for many CSPs, dedicated anything tends to be more expensive to acquire, maintain, and operate.
- They’re more consistent. The way the system operates will be identical across customers, so everything from standard processes to troubleshooting is much easier than if each customer were on their own dedicated system.
- They can leverage economies of scale. Essentially all of the benefits of multi-tenant come from this core truth, when you get right down to it.
You can already see some of the trade-offs here.
- Customers lose a lot of control. In the housing metaphor, an apartment renter can’t reasonably remodel the bathrooms, take down walls, or change the utilities, since that affects all of the tenants.
- Standardization means limitation. If a customer has specific desires, custom apps, or anything else they need running, they may not be able to use them.
- Security has different considerations, some of which can’t be fully eliminated.
This last one is one of the biggest when it comes to FedRAMP. The government, using a CSP, needs to trust that the CSP is secure. Multi-tenant infrastructure means a lot of potential hazards.
These aren’t theoretical, either. There have been multiple breaches in Microsoft Azure that allow access to the underlying infrastructure through credential escalation and other access hacks. Nvidia’s container toolkit had a critical flaw that allowed attackers to step outside the bounds of the containers and access underlying environments. Entire hacker groups have made it their mission to explicitly target multi-tenant environments.
It doesn’t matter how secure your front door is if your neighbor leaves their door unlocked and an attacker uses the balcony to access your home, right?
It’s hard for multi-tenant customers to ensure complete data isolation and security. The government working with the CSP needs that security, but may not be assured of it through their own efforts.
Multi-tenant CSPs often rely on a certain level of standard best practice security amongst their tenants, but without a framework like FedRAMP for them, they can’t guarantee compliance beyond some technological controls.
Is it Even Possible to Get FedRAMP Authorization for a Multi-Tenant CSP?
Fortunately, yes, multi-tenant CSPs can still achieve compliance. They have greater challenges and different areas of emphasis, but it’s fully possible. It’s not even an unreasonable choice, given the advantages of multi-tenant operations, to stick with it rather than shift to a hybrid or single-tenant model for high-needs customers.
You might also wonder if multi-tenant is allowed at High-impact level, since the standards are so much higher. Even if multi-tenant is doable for Moderate impact, is it available for High? Again, yes, it’s possible, though the requirements are steep.
Despite the possibility, some CSPs choose to implement a secondary single-tenant system for high-needs and high-security accounts, specifically to narrow scope and make it easier to achieve authorization. When you see a company offering a general service with a specific “for government” edition (like Google’s Workspace for government, for example), this is often a single-tenant spin-off of a multi-tenant product.
Should your CSP switch to a hybrid or single-tenant mode before seeking FedRAMP authorization, or should you pursue multi-tenant authorization?
There’s no right answer to this question. If you’re interested in our advice, as FedRAMP experts, we’re happy to talk if you drop us a line.
Does FedRAMP have Specific Rules for Multi-Tenant CSPs?
Yes and no.
Specifically, FedRAMP has requirements for security and isolation for government data and accounts. Those requirements can be achieved in various ways, so long as they are validated and can be tested, proven, and monitored.
FedRAMP is based on NIST SP 800-53, and NIST SP 800-53 has some specific controls that apply to multi-tenant CSPs.
SC-3: Security Function Isolation. This control addresses the elevation of privilege threat mentioned above and is part of the High baseline. It requires CSPs to isolate security functions from non-security functions.
SC-7: Boundary Protection. This control addresses the lateral movement of threat actors between accounts on the same system and applies to all impact levels. Section (b) of this control requires that a CSP implement subnetworks for publicly accessible system components that are physically or logically separated from internal networks.
Physical separation is single-tenant; logical separation is multi-tenant.
SC-7(13): Isolation of Security Tools/Mechanisms/Support Components. This is a multifaceted control that addresses elevation of privilege, lateral movement, and information disclosure. It requires the CSP to isolate systems, tools, and components from other system components. Management interfaces and components have to be in separate subnets from operational systems.
SC-39: Process Isolation. Part of all baselines, this control requires that information systems maintain separate execution domains for each executing process. This helps prevent elevation of privilege attacks and more by preventing the modification of executing code from other executing code.
Since the unique threats for multi-tenant operations come from vulnerabilities crossing the barrier between tenants from a less secure to a more secure tenant, the specific additional rules are all focused on isolating and securing individual tenants as much as possible, short of physical separation.
There is a limited selection of security controls. It just goes to show that the bulk of a FedRAMP deployment will remain the same regardless of whether you’re a single-tenant or multi-tenant structured CSP.
How to Secure Multi-Tenant CSPs for FedRAMP Authorization
If you’re a CSP with multi-tenant operations and you’re not willing to shift to a single-tenant system, what should you do to ensure you’re as secure as you can be?
Focus on strong access controls. Every tenant has to have isolated data, yes, but they also need to have isolated access to their data. Systems like multi-factor authentication and prohibitions on account sharing are a must.
Leverage strong encryption. Encryption is both active and passive security. It works actively to prevent cross-process attacks and other threats. It works passively to minimize the potential damage if an intrusion does happen. Using validated encryption algorithms and keeping them up to date is crucial for all FedRAMP deployments, multi-tenant and otherwise.
Be aggressive with continuous monitoring and incident response. Continuous monitoring and incident response are both requirements for FedRAMP, no matter your tenancy situation, but they are especially important when gaps outside of the scope of FedRAMP can lead to compromises within FedRAMP-secured systems. You need detailed, aggressive monitoring and rapid response to the slightest hint of intrusion to minimize any potential damage.
Keep on top of industry news for your components. As mentioned above, the threat to multi-tenant operations doesn’t always come from other tenants, but from the system modules themselves, like the aforementioned Nvidia containers or Azure breaches. It’s important to stay on top of industry news when it relates to component breaches and zero-days, and if your system uses any of them, do everything in your power to address them ASAP.
Consider working on a hybrid solution. While multi-tenant is perfectly fine for your low-security, low-requirement clients, operating with the government and other high-security clients (or within other security frameworks like ISO 27001) will require high standards. It may be beneficial to consider building out a secondary “for government” system that adds single-tenant operations and physical separation to streamline some of the security you’ll need to have implemented.
Work with a 3PAO that understands multi-tenant challenges. When you’re working on implementation, you’re allowed to use a 3PAO as a consultant, though the one that performs your validation audit will need to be different. It can be worthwhile to find a 3PAO or FedRAMP consulting service that understands the unique challenges of multi-tenant operations and knows where to look and what to implement to get everything as secure as possible.
As FedRAMP experts, we at Ignyte can help you in a variety of ways. You can read our blog or listen to our podcast for additional information on a variety of FedRAMP-relevant topics. You can reach out and talk to us directly with questions or work with us on your implementation. You can also use the Ignyte Assurance Platform to track and maintain awareness of your FedRAMP implementation across the board. You can even work with us as your 3PAO.
There’s no reason you can’t successfully deploy FedRAMP on a multi-tenant CSP, even if single-tenant implementation may be deemed “easier” in some ways. Both have high standards, and the differences come down to a few key security controls and a bit of planning. Either way, we can help ensure that you get it done right, done fast.

Dan Page is a seasoned Cybersecurity and Risk Management Executive known for advancing security programs aligned with complex regulatory frameworks and critical business objectives. With over 12 years in information security, his expertise began in the U.S. Army Signal Corps, where he led global communications and secured classified networks supporting Special Operations missions. Post-military, he specializes in security architecture for CUI, ITAR data, and federal cloud workloads. Currently, as Senior Cybersecurity Manager at Ignyte Assurance Platform, Dan guides organizations through compliance with CMMC, FedRAMP, ISO 27001, PCI, and NIST standards. A CISSP, CRISC, CISM, PMP, and ITIL-certified professional, he is also a cybersecurity lecturer and community volunteer advocating workforce development.


 BLUF - Bottom Line Up Front
BLUF - Bottom Line Up Front