 BLUF - Bottom Line Up Front
BLUF - Bottom Line Up Front
Understanding FedRAMP System Boundaries is crucial for enhancing data security in cloud systems. These boundaries define how systems interact and help prevent unauthorized access. Creating diagrams of these boundaries clarifies system relationships and security measures. Important steps involve identifying, documenting, and visualizing system interactions and data access needs while considering external and internal services. This approach aids compliance, improves system efficiency, and strengthens security posture against potential risks.
In the ever-changing world of technology, staying secure is a top priority for many organizations. Identifying and documenting system boundaries is essential for keeping data safe and secure, but what does this mean? In this article, we’ll explore FedRAMP System Boundary, how to identify them, and how to generate FedRAMP System Boundary diagrams. By the end of this guide, you’ll be well-versed in understanding FedRAMP System Boundary and creating diagrams that can help keep your information secure!

1. Introduction to FedRAMP System Boundary
A FedRAMP System Boundary is a line that separates one system from another. To understand FedRAMP System Boundary, it is important first to understand what a system is.
“A system is a set of interacting or interdependent components that form a complex/intricate whole. Systems can be natural or man-made.“
Examples of systems include but are not limited to the human body, ecosystems, businesses, and computer systems.

When dealing with cloud technologies, it is important to define the system boundary. This boundary describes the internal parts of a cloud system and how it connects with external services and systems. It takes into account how federal information and metadata move within the system. The system boundary helps illustrate the extent of control a cloud service provider (CSP) has over the system, including any components or services obtained from external sources or managed by the customer.
FedRAMP and CMMC are crucial frameworks for assessing and improving the security posture of information systems. They leverage the concept of “system boundaries” to establish clear limits and control points within a system. System boundaries define the scope and interactions of a system with other components, helping stakeholders comprehend the system’s security context. By identifying and documenting system boundaries, organizations can implement appropriate security controls, assess risks effectively, and ensure compliance with stringent requirements. The consideration of system boundaries enables organizations to establish robust security measures and enhance the overall security posture of their organizations’ information systems.
Watch a short course formal course on NIST RMF Step 1 – Authorization Boundaries
2. Benefits of Understanding and Creating FedRAMP System Boundaries
When understanding and creating system boundaries, many benefits can be gained. Perhaps the most obvious benefit is that it can help prevent unauthorized access to systems and data. By understanding where the boundary of a system lies, you can more easily control who has access to it and what they can do with it. Additionally, creating system boundaries can also help improve efficiency and performance. Segmenting systems into smaller, more manageable parts can reduce overall complexity and improve resource utilization.
3. Examples of FedRAMP System Boundary Diagrams
There are countless examples of system boundary diagrams. We’ve compiled a few examples below to help you understand how these diagrams can be used. System boundary diagrams can be used to map out the relationships between different systems and their data. For example, a diagram may show System A has access to data in System B but not vice versa. This type of diagram is helpful in understanding which systems have access to sensitive data and which do not.
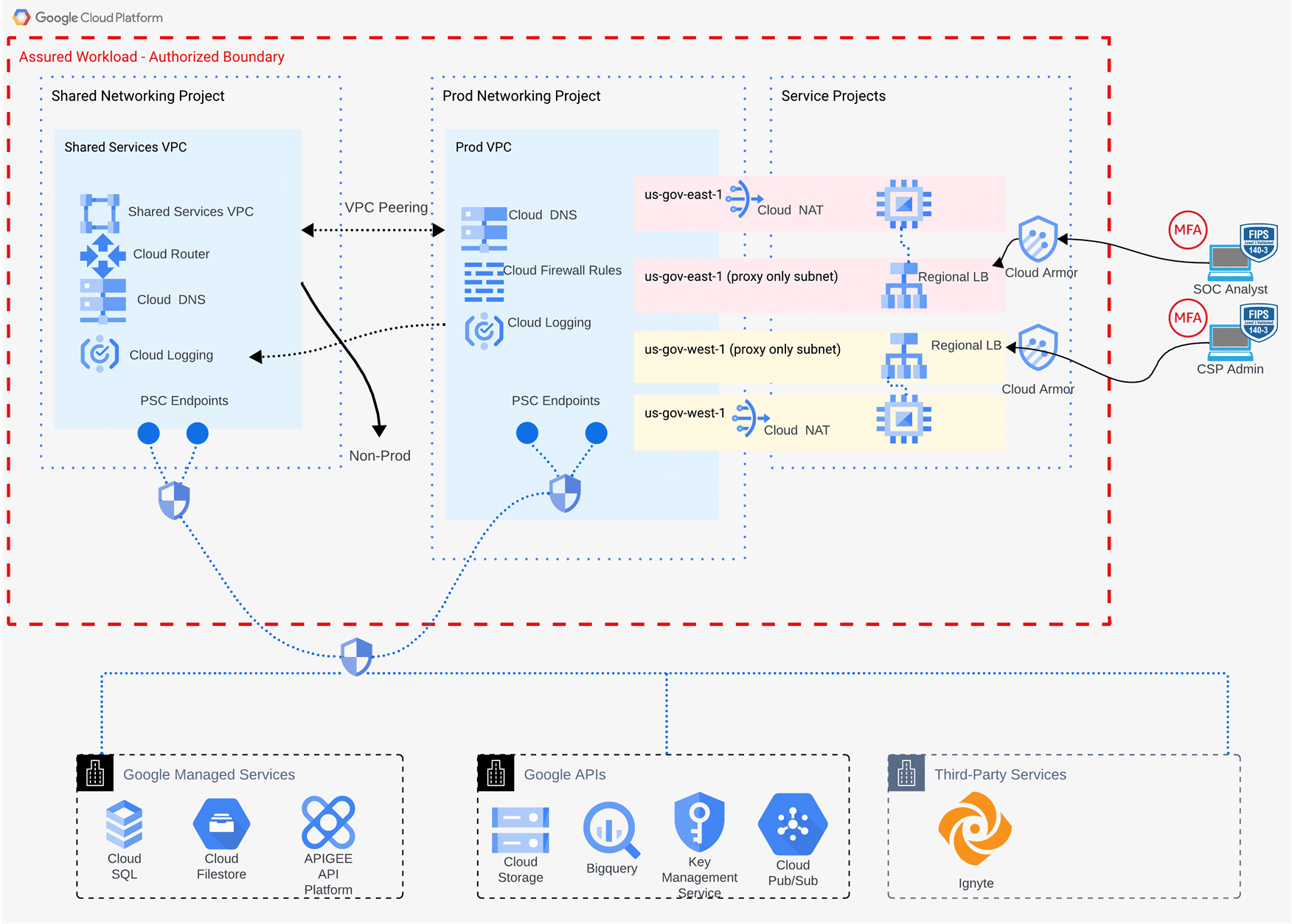
Example system boundary diagram
Another use case for system boundary diagrams is documenting how users gain access to specific systems. For example, a diagram may show that users must first log in to System A before accessing any data in System B. This type of diagram helps understand the security controls in place for each system.

4. Identifying FedRAMP System Boundaries
System boundaries are the dividing line between one system and another.

Once the different types of systems are identified, it is possible to identify potential boundaries between them. This can be done by looking at each system’s resources and information to function properly. If two systems share no resources or information, they are not considered connected and therefore do not have a boundary between them.
Once all potential boundaries have been identified, it is then necessary to document them. This documentation should include a description of each boundary and the rationale for its existence. It should also include any relevant diagrams or other visual aids that will help to understand the boundary better.
Finally, generating an system boundary diagram is important once all boundaries have been documented. This diagram will show which systems can access which resources and information. It is an important tool for ensuring that information and resources are properly isolated and helps prevent unauthorized access.
5. Developing FedRAMP System Boundaries
System boundaries define the scope of a system to be assessed. Understanding system boundaries is important for two reasons: first, because it helps identify the limits of a system, and second, because it can help prevent unauthorized access to a system. They are also critical for understanding the relationships between systems and their shared data. They help visualize these relationships and can be used to generate system boundary diagrams.
Documenting system boundaries is the first step to creating an system boundary diagram. A system boundary diagram visually represents a system’s security perimeter. It illustrates which parts of a system are accessible to which users and what level of access each user has.

To generate a system boundary diagram:
- Start by identifying all the systems needing data access.
- Determine which data each system needs to access.
- Create a diagram showing the relationships between the systems and the data.
- Place a red-dotted line (or a box with a key legend) to shoe the boundary perimeter.
Remember that system boundary diagrams are just one tool for understanding system boundaries. They should be used in conjunction with other tools, such as security audits, to get a complete picture of the relationships between systems and data.
According to the FedRAMP PMO, the following guidance is provided for consideration when documenting the system boundary:
5.1. Federal Information (Data and MetaData) in the Cloud
CSPs must include all federal data generated or received from a federal customer within the authorization boundary of their Cloud Service Offering (CSO). This ensures proper management and protection of sensitive information in compliance with security requirements and policies.
5.2. Interconnections in the Cloud
Agency Authorizing Officials (AOs) thoroughly assess interconnections in cloud technologies to ensure proper protection of federal data and metadata within the system. Cloud technologies rely on interconnections, APIs, and other connections that transmit federal information. It is crucial to disclose these connections and associated risks to the AO through FedRAMP deliverables to maintain transparency and mitigate potential risks to federal information.
5.3. Leveraging External Services with a FedRAMP Authorization
When a Cloud Service Offering (CSO) utilizes an external service that already has FedRAMP Authorization, the CSP can show compliance with FedRAMP/NIST SP 800-53 control requirements by leveraging the capabilities of the external provider. The CSP must document this relationship in the FedRAMP Authorization Package, including the System Security Plan (SSP) and Control Implementation Summary (CIS).
5.4. External Services in the Cloud
Cloud technologies can enhance their functionality by utilizing systems, components, and services from external sources that are not under the direct control of the vendor seeking FedRAMP authorization. It is essential for the Cloud Service Provider (CSP) to clearly communicate these external services to the Authorizing Official (AO) and indicate the potential impact on federal information.
5.5. Corporate Services (out of Scope)
Corporate services are external services utilized by a Cloud Service Provider (CSP) for their internal business operations and are separate from the authorization boundary of the Cloud Service Offering (CSO). These services do not contain any information that would impact the confidentiality, integrity, or availability (CIA) of the CSO.
Lastly, system boundary diagrams can also generate reports showing which users have access to which systems. This type of report is helpful in auditing user access and identifying potential security risks.
6. Conclusion
In conclusion, understanding system boundaries is key to identifying, documenting, and generating system boundary diagrams. It helps us identify areas where security risks may be present and allows us to take steps to mitigate them. By being aware of potential threats and having a clear picture of the different components within our systems, we can avoid any potential issues. With this knowledge, you will be on your way to creating secure environments for your data and applications.



 BLUF - Bottom Line Up Front
BLUF - Bottom Line Up Front