 BLUF - Bottom Line Up Front
BLUF - Bottom Line Up Front
FIPS Validation is the only recognized designation for cryptographic modules, important for FedRAMP and CMMC. It indicates a product has passed conformance tests at an accredited lab. Compliance or certification are not recognized terms. Organizations must use FIPS validated modules to handle government information securely. Many modules moved to historical status due to algorithm retirement, so check if your module is current. Document cryptomodule use in a Crypto Module Reporting Table for data handling.
Here are 5 key takeaways in this post:
- There is only one FIPS Validated Cryptographic Modules designation.
- Validation is what most auditors look for when it comes to FedRAMP and CMMC.
- FIPS Validation means a product has undergone and passed detailed conformance testing at an accredited national laboratory.
- Organizations that have to follow CMMC must use FIPS validated cryptographic modules.
- To be FedRAMP authorized you have to use FIPS validated cryptographic modules in all areas where cryptography is required. This includes the following controls: SC-8, SC-8(1), and SC-28 required.
The Federal Information Processing Standard (FIPS) 140-3 (2019) is “applicable to all federal agencies that use cryptographic-based security systems… and shall be used in designing and implementing cryptographic modules that federal departments and agencies operate or are operated for them under contract.”
In other words, any organization that stores, processes, or transmits certain government information must do so in a way that conforms to the FIPS standard.
What does that mean for CMMC and FedRAMP?
CMMC is designed to create environments capable of safeguarding government information, organizations that have to follow CMMC must use FIPS validated cryptographic modules.
In much the same way, organizations that offer cloud services and products to the U.S. government must be FedRAMP authorized. To be FedRAMP authorized you have to use FIPS validated cryptographic modules.
You’ll notice that we didn’t use the words certified or compliant. That’s because there is only one FIPS designation – validated. Validation is what auditors look for when it comes to FedRAMP and CMMC. Not certification or compliance. But let’s take a closer look at the 3 words typically used when discussing FIPS and how these words are interpreted.
FIPS Certified
FIPS certified means the same thing as validated so long as it is used within the context of a cryptographic module that has gone through the necessary validation process from a NIST approved lab.
FIPS Compliant
This is the one that causes trouble. In fact, many respondents in a recent survey conducted by MTSI about FIPS interpretations offered this explanation, “compliance means that different components of a product have received FIPS validation, but the product in its entirety has not passed testing or has not been tested at all.”
Unfortunately, the word “compliant” is only used once in the official FIPS document, and it’s in reference to the Implementation Schedule. That is, there is no official use or definition of the phrase FIPS compliant. The industry has adopted this phrase on its own without any factual basis for its use.
FIPS Validated Cryptographic Modules
In the same survey, respondents said this about validation, “FIPS Validation means a product has undergone and passed detailed conformance testing at an accredited national laboratory.”
This is the correct understanding of the FIPS 140-3 standard.
To further demonstrate this point, all you have to do is read through the official document. If you read carefully, you’ll notice that any language that speaks to a cryptographic module adhering to the requirements of FIPS 140-3 uses the word “validated”.
Not certified. Not compliant.
Historical Status due to SP 800-56A rev3 transition
On July 1, 2022, many FIPS 140 validated cryptographic modules moved to historical status due to retirement of a key exchange algorithm. It is critical to review if your crypto module is current or have been moved to the historical status for the purpose of achieving your FedRAMP and DISA IL based ATO for your CSP. For more details please review the Implementation Guidance for FIPS 140-2 and the Cryptographic Module Validation Program.
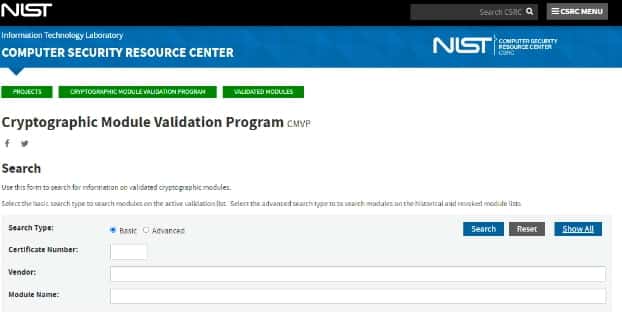
You now have to verify whether the cryptographic module in use is acceptable or not by referencing the NIST CMVP site for cryptomodules with a “Historical Reason” indicating SP 800-56A rev3 transition. The picture below is a snapshot of the NIST CMVP Search function. On this site you can search for information on validated cryptographic modules by Vendor Name, Module Name, or by the certificate number if you have it.
Building a Crypto Module Reporting Table
A crypto module reporting table (CMRT) documents and describes all the cryptomodules that are currently implemented (not planned) in each area and for each flow of data. This means All Data in Transit (DIT), meaning all data traversing the boundary – like backups to storage, and data moving inside the boundary – like server to server. Additionally, the CMRT should include all Data at Rest (DAR), inclusive of all areas where there is government data and metadata.
Below is an example of a Crypto Module Reporting Table for Data in Transit (DIT)

Below is an example of Crypto Module Reporting Table for Data at Rest (DAR)

Conclusion
Ignyte believes there is only one (1) FIPS designation – FIPS Validated. This is the language the authors of the standard use. It is the language NIST uses when referencing FIPS requirements. And it’s the verbiage the Open-Source Control Assessment Language (OSCAL) uses.
Using any other term just creates confusion, and Ignyte prides itself on transparent communication in all aspects of our work.
Does your system use FIPS validated cryptography? If you don’t know, contact us.


 BLUF - Bottom Line Up Front
BLUF - Bottom Line Up Front